Insights & Research
The Dr.Binary Blog
Deep dives on agentic binary analysis, AI-powered reverse engineering, malware defense, and the techniques behind the platform.
May 12, 2026
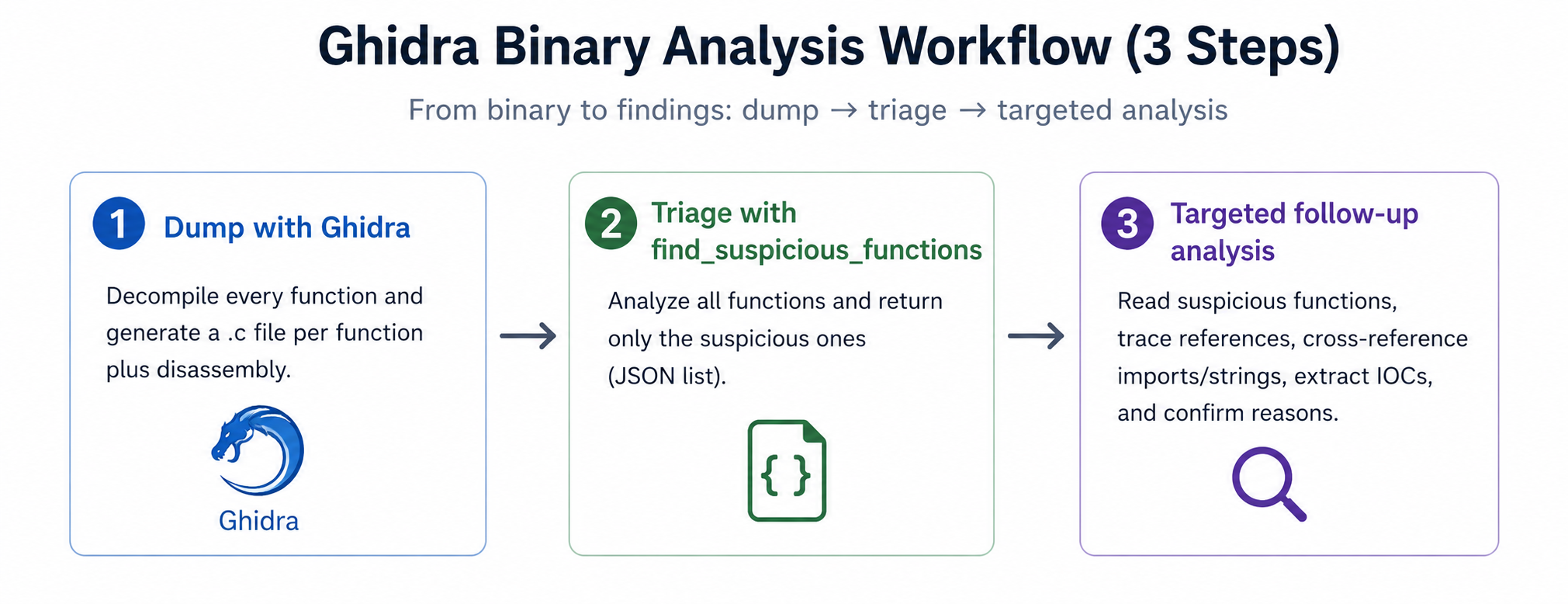
Lessons from Building Agentic Binary Analysis, Part 1: LLMs Skim, They Don't Explore.
The most fundamental failure mode of LLM-powered binary analysis: models evaluate binaries by their most obvious features and stop there. This post walks through how Dr. Binary addresses it with an exhaustive analysis tool that processes every function before the LLM draws any conclusions.
Read more
October 8, 2025
Agentic Binary Analysis: When AI Becomes the Analyst
Exploring how autonomous AI agents are revolutionizing binary code analysis through self-directed reasoning, collaborative multi-agent systems, and adaptive threat detection strategies that operate without human intervention.
Read more
March 5, 2025
DeepDiff: Next-Generation Binary Diffing for Precise Vulnerability and Patch Detection
We're excited to announce the launch of DeepDiff, Deepbits' groundbreaking solution for vulnerability detection and binary diffing. DeepDiff represents a major leap forward in security analysis. It helps security researchers, reverse engineers, and development teams to pinpoint vulnerable functions and generate precise diffing views across binary files with unmatched accuracy.
Read more
February 13, 2023
How Binary Code AI Changes Malware Defenses?
Existing commercial malware detection engines have a relatively low first-day detection rate for newly discovered samples, and it takes two to three days to gradually reach a detection rate of more than 90%. This leaves a large attack surface for malware. To solve this problem, we developed a new technique that can identify new malware at first sight, without the need for periodic retraining of machine learning models.
Read more
June 23, 2020
A Fast and Accurate Disassembler based on Deep Learning
A disassembler takes a binary program as input and produces disassembly code and some higher-level information, such as function boundaries and control flow graphs.
Read moreMay 9, 2019
A Comparative Review of Embedding based Binary Code Search Techniques
A Comparative Review of Embedding based Binary Code Search Techniques
Read more